Your cart is currently empty!
Iran Hackers Expose Personal Photos From Kash Patel Email Account

A leak like this does not need to expose state secrets to become politically explosive.
When reports emerged that Iran-linked hackers had accessed FBI Director Kash Patel’s personal email and released a cache of private photos, travel details, and old correspondence online, the story instantly became bigger than one man’s inbox. It became a snapshot of modern power in the digital age, where the most effective attacks are not always the most sophisticated. Sometimes, humiliation itself is the weapon.
According to Reuters and CNN’s reporting, the material appears to have come from Patel’s personal account rather than official FBI systems, and U.S. officials have stressed that no government information was exposed. Even so, the optics are brutal. The director of the FBI, the country’s top domestic law enforcement agency, has found himself at the center of a cyber breach that seems designed less to steal classified intelligence and more to send a message: no one is untouchable anymore.
A Personal Hack That Became a Political Event
The hackers, operating under the name Handala Hack Team, published more than 300 emails and a set of personal images they claimed were taken from Patel’s account. Among the material described in coverage were casual photos, personal snapshots, travel-related documents, and older correspondence dating back years before Patel became FBI director.
That distinction matters, and the FBI moved quickly to emphasize it. The bureau said the exposed information was historical and did not involve government systems or government data. On paper, that should have lowered the temperature.
But in politics, paper explanations rarely outrun public perception.
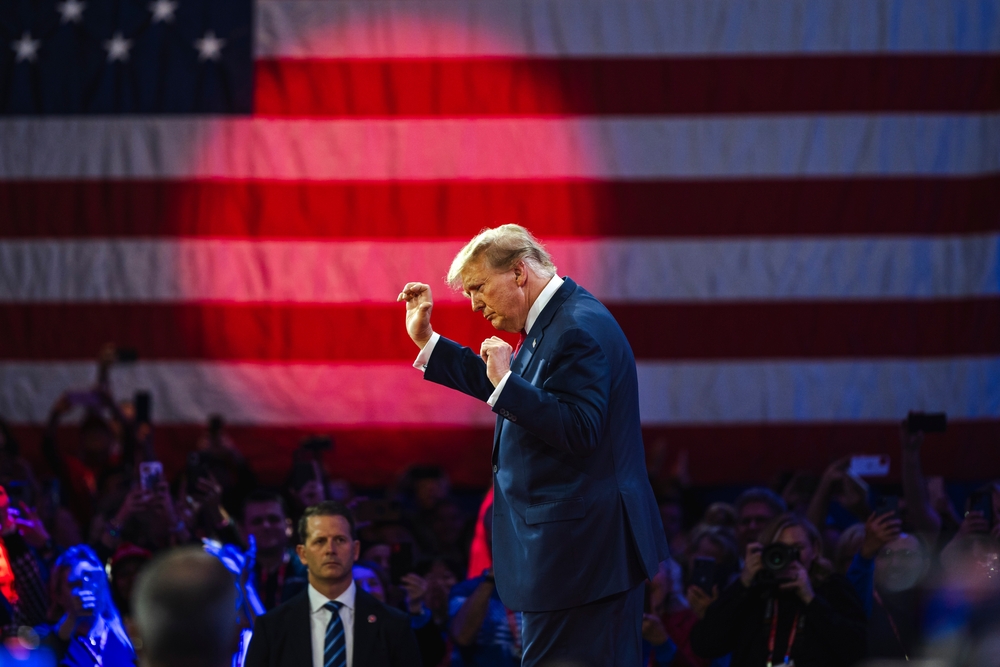
Patel is not just another federal official. He is one of the most politically recognizable figures in Donald Trump’s orbit, a man whose rise has been closely tied to battles over the so-called deep state, intelligence agencies, and the credibility of U.S. law enforcement institutions. That means any breach involving him was always going to land as more than a cybersecurity incident. It was bound to be interpreted as symbolism.
And that is exactly what makes this leak politically potent.
This was not framed by the hackers as a quiet intelligence operation. It was presented as a public takedown. The apparent goal was not simply to obtain information, but to make an example out of a high-profile American official and, by extension, the political establishment around him.
Why This Matters Even if No Classified Files Were Taken

One of the easiest mistakes in stories like this is assuming that if no classified material was stolen, the incident is mostly embarrassing and little more.
That view misses how cyber conflict actually works in 2026.
A modern hack-and-leak operation can serve several purposes at once:
First, it creates spectacle. Once personal photos and inbox fragments hit the internet, the target loses control of the narrative almost immediately.
Second, it tests vulnerability. Even if the published files are mundane, the breach itself proves access was possible.
Third, it delivers psychological impact. Public officials are reminded that their private lives can be dragged into geopolitical conflict with very little warning.
That last point may be the most important. Reuters cited cybersecurity experts who said operations like this are intended to embarrass U.S. officials and make them feel vulnerable. That phrasing is worth sitting with, because it captures something many political headlines flatten too quickly.
This was not just about Kash Patel.
It was about pressure.
Pressure on an administration.
Pressure on public confidence.
Pressure on the idea that America’s most powerful institutions are still fully in control.
In that sense, the breach did exactly what it was meant to do. It created a spectacle that forced both the FBI and the White House ecosystem to react, explain, reassure, and defend.
The Bigger Backdrop is the Worsening U.S.-Iran Cyber Conflict

To treat this as an isolated leak would be misleading.
The Patel breach appears to fit into a broader escalation in the long-running digital confrontation between Iran and the United States, one that has intensified as tensions in the Middle East have spilled into cyberspace. In recent reporting, Handala has also been linked to claims involving attacks on U.S. corporate and defense-related targets, including healthcare and defense-sector entities.
That pattern matters because it shows how cyberwarfare often unfolds far from the battlefield and far from military headlines.
Not every retaliatory move comes in the form of missiles or troop deployments. Some of it comes through:
- targeted leaks
- pressure campaigns
- disinformation pushes
- strategic embarrassment
- attacks on infrastructure and private-sector networks
That is what makes cyber conflict so politically slippery. It rarely arrives with a clean beginning or a dramatic declaration. Instead, it accumulates. A leak here. A disruption there. A threat campaign somewhere else. Before long, the line between national security and everyday digital life starts to blur.
In Patel’s case, the leak lands at a moment when Washington is already on edge over how Iranian-linked actors might retaliate against U.S. officials and institutions. That gives this story a significance beyond the salacious details some corners of the internet will inevitably fixate on.
The real story is not that there were private photos.
The real story is that cyber retaliation now routinely includes the personal lives of senior officials as a legitimate theater of conflict.
Kash Patel’s Role Makes the Fallout Harder to Contain

If this had happened to a lower-profile bureaucrat, it likely would have remained a serious but niche security story.
But Patel is a politically loaded figure.
To supporters, he represents an aggressive attempt to wrest control of federal institutions away from the old national security establishment. To critics, he embodies the politicization of law enforcement and intelligence culture under Trump-aligned leadership.
That means the breach instantly became a Rorschach test.
For critics of the administration, it looks like another sign of dysfunction and sloppiness in an era defined by performative toughness but recurring operational embarrassment. They will point to the symbolism of the FBI director himself being digitally compromised and argue that image management has overtaken serious institutional discipline.
For supporters, the breach will likely be framed as proof that Patel is a target precisely because he is viewed as threatening to America’s adversaries and entrenched interests. In that telling, the hack becomes not a sign of weakness, but evidence of how aggressively hostile actors want to damage him.
Both readings are politically useful. Neither fully captures the underlying problem.
The uncomfortable truth is that modern cyber vulnerability is not always ideological. It is often deeply ordinary.
That is part of what makes incidents like this so unsettling. The most powerful people in the world still rely on the same fragile digital habits as everyone else: old email accounts, forwarded documents, reused passwords, cloud-stored memories, years of archived correspondence, and personal devices that quietly become historical records of their lives.
Power does not erase digital mess. It just raises the stakes when that mess is exposed.
America Has Seen This Playbook Before

One reason this story feels instantly familiar is that the U.S. political system has already been shaped by years of hack-and-leak scandals.
Americans do not need a tutorial on how personal email accounts can become political weapons. The 2016 election burned that lesson into the public consciousness. The hacking of John Podesta’s Gmail and the release of his messages through WikiLeaks changed the rhythm of that campaign and became one of the defining examples of how cyber intrusion can reshape politics without firing a single shot.
There have been other examples too, from the breach of former CIA Director John Brennan’s personal AOL account to repeated attempts by foreign actors to target advisers, campaign staff, and politically connected operatives.
The pattern is no longer surprising. What is striking is how normalized it has become.
That normalization carries its own danger.
Every time a breach is waved away as embarrassing but not catastrophic, the threshold for alarm quietly rises. Public attention narrows to whether the leaked material is scandalous enough to trend, rather than whether the intrusion itself reveals a strategic vulnerability.
That is how democracies get desensitized.
The damage is not only in what was exposed. It is also in how often the public now shrugs at the fact that foreign-linked actors can still reach deep into the personal digital lives of people at the center of American power.
The Optics Are Especially Bad for Trump-World Politics
The politics here are impossible to separate from Donald Trump’s broader brand.
Trump and many of his closest allies have long built their political appeal around a promise of strength, disruption, and dominance. They have often portrayed themselves as tougher, more decisive, and more security-minded than the institutions and political figures they replaced or attacked.
That is why this story cuts so sharply.
An FBI director tied closely to Trump-world politics being publicly embarrassed by Iran-linked hackers is not just a security issue. It is a branding problem.
It creates a visual contradiction between the image of control and the reality of exposure.
And in modern politics, image is not superficial. It is structural.
A leak like this feeds a narrative that America’s adversaries understand something uncomfortable about the current era: attention is often easier to manipulate than systems are to destroy. You do not need to shut down the FBI to make the FBI look penetrable. You just need to make the person at the top appear reachable.
That is why personal digital breaches have become so politically effective. They collapse the distance between the symbolic and the strategic.
A few photos and a handful of inbox records can do what a dense intelligence report cannot. They can make power look small.
What This Says About the Future of Political Warfare

The easiest version of this story is the tabloid version: private photos leaked, powerful official embarrassed, internet reacts.
The more important version is harder to package but much more revealing.
We are watching the continued evolution of political warfare into something more intimate, more psychological, and more difficult to contain.
In the past, national security was often imagined as something housed in secure facilities, classified networks, and official channels. That model still matters, but it is incomplete. Increasingly, the vulnerable surface area of power lives in personal inboxes, private cloud accounts, old photo archives, and digital leftovers from years before someone ever held office.
That creates a strange democratic paradox.
The same technologies that make leaders more reachable, more visible, and more connected also make them more porous. The private and the political are no longer cleanly separable. And hostile actors understand that better than most voters do.
That means the future of political scandal may not always begin with ideology, corruption, or policy failure. Sometimes it will begin with access. Sometimes it will begin with metadata, screenshots, and an old account that was never fully locked down.
That should concern more than one administration or one party.
Because if foreign-linked actors can repeatedly turn the personal digital lives of U.S. officials into pressure points, then the real issue is not just one leak. It is the architecture of vulnerability itself.
A Humiliating Breach, and a Revealing One
There is a temptation in stories like this to reduce everything to ridicule. That temptation is understandable. Public figures are often mocked most when they are caught in moments of contradiction, and there is obvious irony in the FBI director becoming the subject of a very public digital compromise.
But the deeper lesson is not really about irony.
It is about exposure.
Not only Patel’s exposure, but America’s.
The breach appears to have involved old and largely personal material. That matters. It also does not fully resolve the problem. If anything, it reveals how much damage can be done without touching a classified file.
A geopolitical rival or proxy does not always need your secrets.
Sometimes, all they need is your vulnerability.
And in an age where politics is driven as much by spectacle and perception as by policy itself, that may be enough.
The release of Kash Patel’s personal photos will likely cycle through the internet as one more surreal headline in a year already full of them. But once the memes fade and the outrage shifts elsewhere, the underlying warning will remain.
The digital battlefield is no longer somewhere else.
It is in inboxes, phones, cloud drives, and forgotten accounts. It is in the quiet overlap between the personal and the political. And as this episode shows, that overlap is now one of the most contested spaces in modern power.
For all the noise around this leak, that is the part Washington should be taking most seriously.
